IT Role-in-Review - Security AnalystLearn about the top skills and competencies companies look for when searching for a Security Analyst.
In today’s world, cybersecurity is a priority for most companies. As the digital transformation across industries grows, more companies are exploring ways to ensure the protection of their proprietary information and systems. A Security Analyst resume (also known as cybersecurity analyst or information security analyst) has a vast array of responsibilities, including analyzing data to determine security risks, creating policies and procedures, and training other personnel on security issues.
Are you a Security Analyst who is looking to transition to an IT professional career or someone fresh out of college searching for the perfect IT career path that fits your skills? Having difficulty streamlining and optimizing your career documents (Resume, Cover Letter, LinkedIn Profile) with the essential keywords, your relevant accomplishments and experience? Interested in following an IT career path in cybersecurity but not sure how to effectively communicate transferable experience and skills in a way that fits this role? This month’s Role-In-Review article provides useful information for the Security Analyst’s IT professional career. Continue reading to learn about the top competencies, capabilities, and skills companies look for when searching for this essential IT role. Use these insights and examples provided to begin optimizing your career documents. ⇒ Role Description: what would a Security Analyst normally do? How do they support technology projects and what value do they create? A Security Analyst is an integral position in companies across all fields. Companies with corporate databases, financial information and office networks all need security analysts to protect the large amounts of information being stored, shared, or used. Security Analysts protect a company’s network and systems from outside risks, monitor computer infrastructure, and maintain confidentiality and availability of software and information used by the company. They identify, evaluate and recommend security controls to reduce cybersecurity risks. The following is a general role description of a Security Analyst: The Security Analyst works to protect network and proprietary / sensitive information, identifies and corrects flaws in the security system, creates security policies and procedures, and improves the overall compliance with security regulations. All of your career documents should include an introduction that demonstrates how you master the core expectations of a security analyst and what unique value you bring to the hiring company. For more tips on optimizing your introduction, visit our previous post on how to create an effective IT professional profile introduction (Resume and LinkedIn). ⇒ What are the business / technology areas and type of projects a security analyst can support? The following are just a few high demand specialty areas security analysts we have worked with possess.
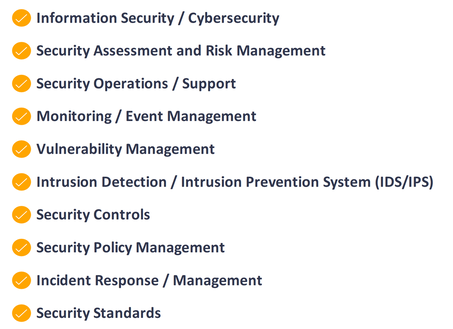
⇒ What are the top competencies hiring companies look for? At IT Career Transformation, we develop a Target Role Analysis for our clients’ targeted IT roles to identify the appropriate keywords and competencies. It is essential that keywords and core competencies are included as many times as possible throughout all career documents. You can include these in your Introduction, Key Areas of Expertise / Competencies and Professional Experience sections. This highlights what sets you apart from other candidates and the unique value you can bring to hiring companies. Here are the top ten core competencies hiring companies look for in a Security Analyst:
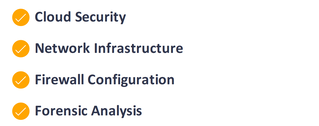
A Security Analyst can specialize in different information/cybersecurity domains such as Application Security, Vulnerability Management, Network Security, Security Assessment / Risk Management, and Policies and Procedures. Specific areas of specialty depend on the hiring company’s particular industry and technology environments. Your career documents should contain specialties you possess and are relevant to your target role. Here are some examples of Security Analyst specialty areas in high demand:
⇒ Don’t forget to include your soft skills. In today’s competitive job market, companies also look for people with the right soft skills in all IT roles. It is essential to include those interpersonal / leadership skills in which you excel throughout all of your career documents. Include terminology such as relationship development / management, adaptable and self-confidence. Here are a few more examples of soft skills recruiters and hiring managers look for in a Security Analyst: Meticulous & Detail Oriented | Analytical Problem Solver | Self-Motivated | Strong Verbal and Written Communication skills | Collaboration | Creative Leadership | Multitasking & Adaptability ⇒ What type of desired capabilities, professional experience and accomplishments are hiring companies looking for when searching for a Security Analyst? Most often, these are included in the “Responsibilities” or “What you will do” sections of the job description. Here are few examples of Security Analyst desired capabilities in high demand:
It is essential to write accomplishment statements in a form of “action—impact—results,” highlighting the value you created to your employer or customers, ideally providing tangible results (numbers) from your projects. Here is an example of an optimized accomplishment statement. Maintain and configure vulnerability management tools, perform system vulnerability scans, and collaborate with business and technical teams to analyze results and implement remediations to existing / new solutions, reducing program’s security incidents by 40%. ⇒ What are the technical skills hiring companies look for when searching for a Security Analyst? This depends on the business, technology stack and development (Agile / Waterfall) and hosting (cloud / on-premises) environments the hiring company uses. Here are some of the software skills often desired for a Security Analyst: Proofpoint, Tcpdump, Wireshark, Nmap, Splunk, Kali Linux, AWS, Azure, GCP, Cloudflare, Windows and Linux operating systems We hope this review provides useful recommendations for you to use and share with your friends while optimizing career documents. If you are considering an IT career path as a Security Analysist and need help transforming your resume into an IT resume, be sure to visit our previous blog article: Transition to IT - Resume writing tips. You can also visit our Services page and look into IT Career Transformation’s services; in particular—the “Target Role Analysis” service—for a complete report that includes a list of tailored recommendations that are specific to your target IT role and specific areas of specialties.
IT Career Transformation is devoted to helping IT professionals and leaders advance their career. We work with IT professionals from entry level to senior management and all types of IT roles to create the Optimum IT Professional Resume, Cover Letter and LinkedIn Profile, optimized with keywords relevant to the target IT role and specialty areas. We provide specialized career development services that help IT professionals accelerate their job search.
Do you need help optimizing your resume to your target IT role? Visit us at https://www.itcareertransformation.com/ for more information and to schedule your complimentary initial consultation.
0 Comments
Your comment will be posted after it is approved.
Leave a Reply. |
IT Career Transformation - Connecting Talent with IT Industry Demand
IT Career Transformation
Atlanta, GA
(470) 210-7955 - [email protected]
Copyright © 2022 All Rights Reserved